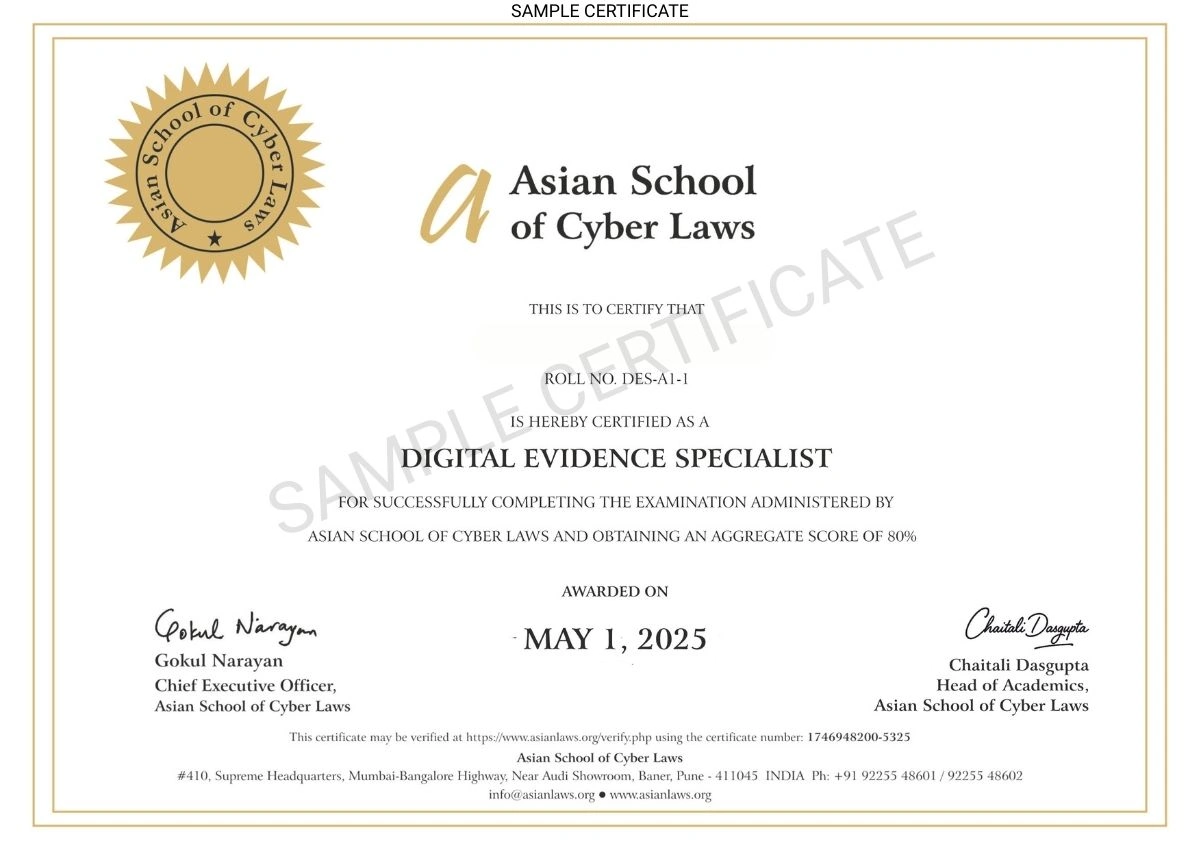
Digital Evidence Specialist
Today, most crimes and disputes involve electronic data, making the study of digital evidence essential for ensuring accurate investigations and legal proceedings. With the rise of cybercrime, online fraud, and digital transactions, understanding how to collect, analyse, and present digital evidence in a court of law is crucial.
Course info at a glance
Language: English
Level: Advanced
Duration: 3 months
Next Batch Starts: 01 May 2026
Course Fee: INR 6,000 + 18% GST
Requirements: Higher Secondary Pass Grade. General Internet and Social Media Awareness
Assessments: A 100 mark open-book ONLINE exam. Score at least 40% to pass. You will have 1 year from your admission date to complete the course. Beyond this, you will be required to take re-admission.
Last date for receipt of application and fee: 30 Apr 2026